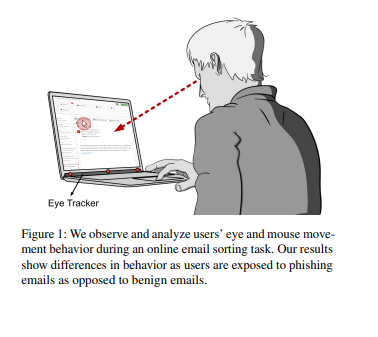
Users are the last line of defense as phishing emails pass filter mechanisms. At the same time, phishing emails are designed so that they are challenging to identify by users. To this end, attackers employ techniques, such as eliciting stress, targeting helpfulness, or exercising authority, due to which users often miss being manipulated out of malicious intent. This work builds on the assumption that manipulation techniques, even if going unnoticed by users, still lead to changes in their behavior. In this work, we present the outcomes of an online study in which we collected gaze and mouse movement data during an email sorting task. Our findings show that phishing emails lead to significant differences across behavioral features but depend on the nature of the email. We discuss how our findings can be leveraged to build security mechanisms protecting users and companies from phishing.
https://arxiv.org/pdf/2305.17044.pdf
How to detect phishing emails with eye and mouse tracking
Phishing emails are one of the most common and dangerous cyber threats, as they can trick users into revealing sensitive information, opening malicious attachments, or clicking on fake links. Phishing emails often use various manipulation techniques, such as impersonating a trusted sender, creating a sense of urgency, or appealing to emotions, to persuade users to perform the desired actions. However, these techniques may also affect users’ behavior in subtle ways, even if they do not fall for the phishing attempt. For example, users may spend more time or attention on phishing emails, or exhibit different patterns of eye and mouse movements, compared to benign emails.
A recent paper by Yao et al. investigates how phishing emails influence users’ eye and mouse movements during an email sorting task. The authors conducted an online study with 60 participants, who were asked to sort 30 emails into three categories: work, personal, and spam. The emails included 10 phishing emails, 10 benign emails, and 10 spam emails. The phishing emails were designed to use different manipulation techniques, such as authority, scarcity, reciprocity, or social proof. The authors used GazeRecorder, a webcam eye-tracking software, to record the participants’ eye and mouse movements during the task. They also collected the participants’ self-reported ratings of the emails’ trustworthiness, urgency, and emotional valence.
The authors analyzed the eye and mouse movement data using various features, such as fixation duration, saccade length, pupil dilation, mouse speed, and mouse distance. They found that phishing emails led to significant differences in some of these features, depending on the nature of the email. For example, phishing emails that used authority or scarcity techniques resulted in longer fixation durations and shorter saccade lengths, indicating more focused attention. Phishing emails that used reciprocity or social proof techniques resulted in larger pupil dilations and faster mouse speeds, indicating more arousal or stress. The authors also found that the eye and mouse movement features correlated with the participants’ ratings of the emails’ trustworthiness, urgency, and emotional valence.
The authors suggest that eye and mouse movement data can be used to detect phishing emails and to provide feedback or warnings to users. They also discuss the limitations and challenges of using webcam eye-tracking for phishing detection, such as the accuracy, privacy, and usability issues. They propose future directions for improving the eye-tracking technology and for exploring other behavioral indicators of phishing.
This paper demonstrates how eye and mouse tracking can reveal the hidden effects of phishing emails on users’ behavior and cognition. It also shows how GazeRecorder can be used to collect and analyze eye and mouse movement data in an online setting.